Noticias, Consejos, Laboratorio de seguridad
3AM Ransomware Backs Up LockBit In Cyberattacks
Investigadores de ciberseguridad han descubierto una nueva familia de ransomware llamada 3AM. Attackers attempted to use it as an alternative attack…
What Is Identity Theft & How to Protect Against It
El robo de identidad es un problema importante que afecta a millones de personas cada año., ya sea a través de información de tarjetas de crédito robadas o cuentas fraudulentas. It’s a…
Google Fixes Critical Vulnerability in Chrome, Exploited in the Wild
Google lanzó una actualización de seguridad urgente para su navegador Chrome. The patch contains the fix for CVE-2023-4863, a heap buffer…
Spyware in Fake Telegram Apps Infected Over 10 million Users
Es importante tener cuidado al utilizar mods de Messenger.. There have been reports of spyware disguised as modified versions…
Mirai variant «Pandora» infects Android TV for DDoS attacks.
Detectada una nueva variante de la botnet del malware Mirai, Infectando decodificadores de TV Android de bajo costo. They are extensively…
Fake DDoS App Targets Pro-Ukrainian Hacktivists
Grupo de análisis de amenazas de Google (ETIQUETA) specialists reported that the Russian-speaking…
CloudMensis Malware Attacks MacOS Users
Los expertos de ESET han descubierto el malware CloudMensis, which is used…
«Your Account Has Been Locked»: Top 5 Signs of a Phishing Scam
The topic of our article will be how to understand…
Cybersecurity Researchers Discovered a New Phishing Kit targeting PayPal Users
Akamai has identified a new phishing kit that is being…
DDoS Booter & IP Stresser
The toolkit of cybersecurity specialists in companies does not consist…
How to Prevent Email Spoofing in 2022
Email Spoofing Email spoofing or spoofing email is the forgery…
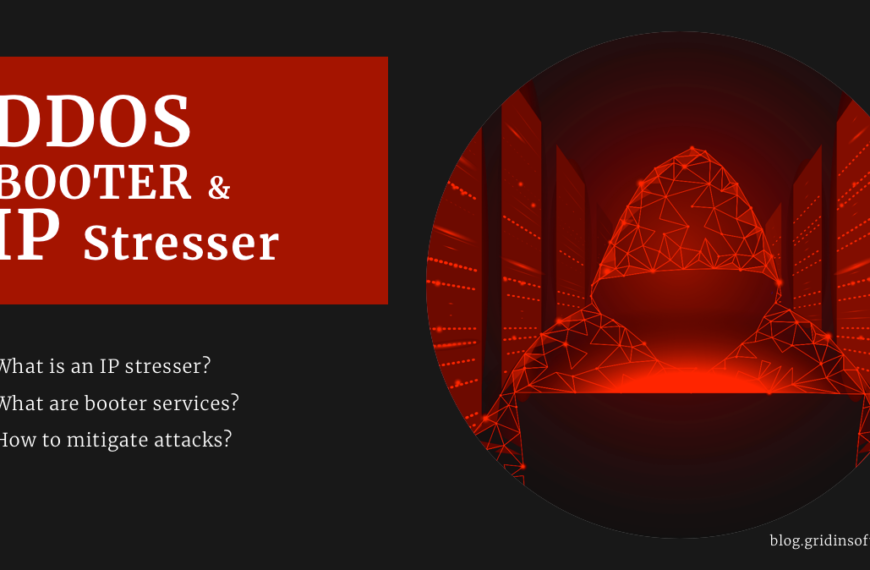
SASE vs Zero Trust – What is Best?
A medida que la tecnología evoluciona, Los piratas informáticos se vuelven cada vez más sofisticados., remote working has…
Microsoft Releases PoC Exploit to Escape MacOS Sandbox
Microsoft has detailed a recently patched vulnerability affecting Apple operating…
5 Security Mistakes You’re Making On Social Media
Leading digital life on various social media platforms can sometimes…
DDoS Attacks: 6 Tried-and-Tested Methods How to Prevent It
Ataques DDoS: 6 Tried-and-Tested Methods How to Prevent It Before…
100% Disk Usage Windows 10: How to Fix Disk Issue
100% disk usage is a widespread problem among Windows users…
U2K Ransomware Strikes, Thousands Of Victims
ransomware U2K, probablemente la estrella en ascenso en el campo del ransomware,…