Noticias, Consejos, Laboratorio de seguridad
Botnet of 400,000 Devices Used as Proxy Nodes Uncovered
Los ciberdelincuentes utilizaron malware sigiloso para crear una botnet de 400,000 servidores proxy. Although the company providing the proxy services claims…
HiatusRAT Used in Attacks on Taiwan Companies and U.S. Military
Los recientes ataques contra sistemas militares estadounidenses y empresas de Taiwán se distinguen no sólo por la valiente elección del objetivo, pero también…
Phishing With Hacked Sites Becomes a Massive Menace
Los actores de amenazas comenzaron a utilizar sitios web comprometidos con fines de phishing con mucha más frecuencia. Such worrying statistics popped up in several recent…
Beware of Cryptocurrency Recovery Scams
Recientemente, the FBI reported increased scammers posing as companies offering to recover stolen cryptocurrency funds. These cunning intruders assure victims…
Back to School Scams Expand As August Begins
A medida que se acerca la nueva temporada escolar, Los estafadores se dirigen a los estudiantes y sus padres.. They use social engineering and offer free school…
Copyright Claims Used as Bait by LockBit 2.0 Affiliates in Korea
A new type of email-bait has been invented by the…
How to Prevent Crimeware Attacks: Users` Guide
Puede que te encuentres con el término «software criminal» and understandably get…
NCC Group’s May 2022 Threat Report Reflects Conti’s End
NCC Group’s monthly report on cyber threats features some curious…
Privacy Access Tokens to Replace CAPTCHA Real Soon
CAPTCHA, a well-known test for website visitors to prove they…
Chinese Hackers Use Ransomware As a Cover for Espionage
Secureworks experts have found that Chinese hackers from two groups…
8 Symptoms Of Adware: How to Avoid it
¿Qué significa el software publicitario?? It is an agressive software whose…
Google Report Companies Creating Mobile Spyware for Governments
Google Reveals An Italian Company to Sell Android and iOS…
Microsoft Accuses Russia of Cyberattacks against Ukraine’s Allies
En el último informe sobre seguridad de la información global, Microsoft accuses…
WiFi-Hacking by Neighbours is Rampant in the UK, Research Says
El hackeo de WiFi por parte de vecinos está muy extendido en el Reino Unido, La investigación dice…
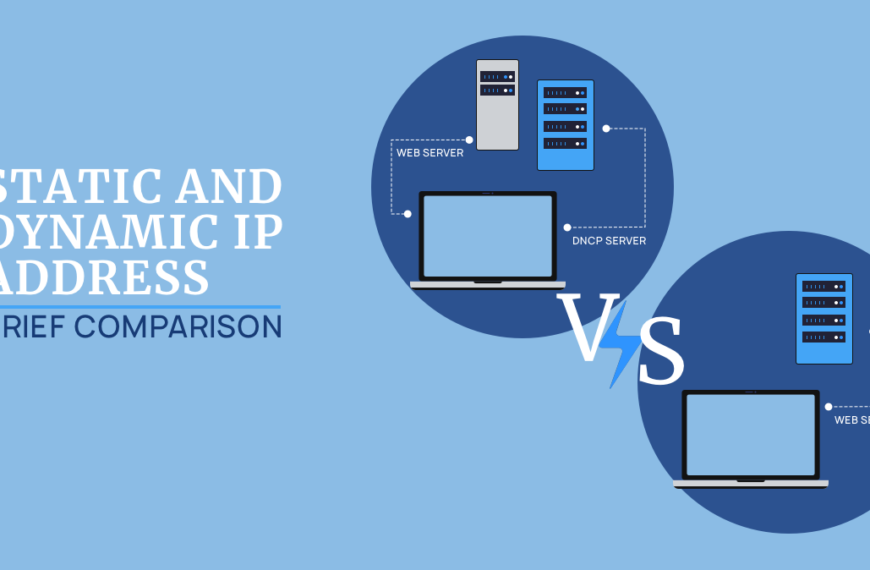
Static And Dynamic Ip Address: Brief Comparison
Internet se basa en direcciones IP. They are divided…
DNS Cache Poisoning and DNS Spoofing
DNS poisoning and spoofing is a cyberattack that exploits vulnerabilities…
Nine Web Scammers Arrested by Dutch Police in a Europol Operation
Nine Internet scammers arrested in the Netherlands during Dutch-Belgian joint…